![Smart Contract Attacks [Part 1] - 3 Attacks We Should All Learn From The DAO | by Pete Humiston | HackerNoon.com | Medium Smart Contract Attacks [Part 1] - 3 Attacks We Should All Learn From The DAO | by Pete Humiston | HackerNoon.com | Medium](https://miro.medium.com/v2/resize:fit:988/1*UeDgMZo2n0skHzgkl352zQ.png)
Smart Contract Attacks [Part 1] - 3 Attacks We Should All Learn From The DAO | by Pete Humiston | HackerNoon.com | Medium

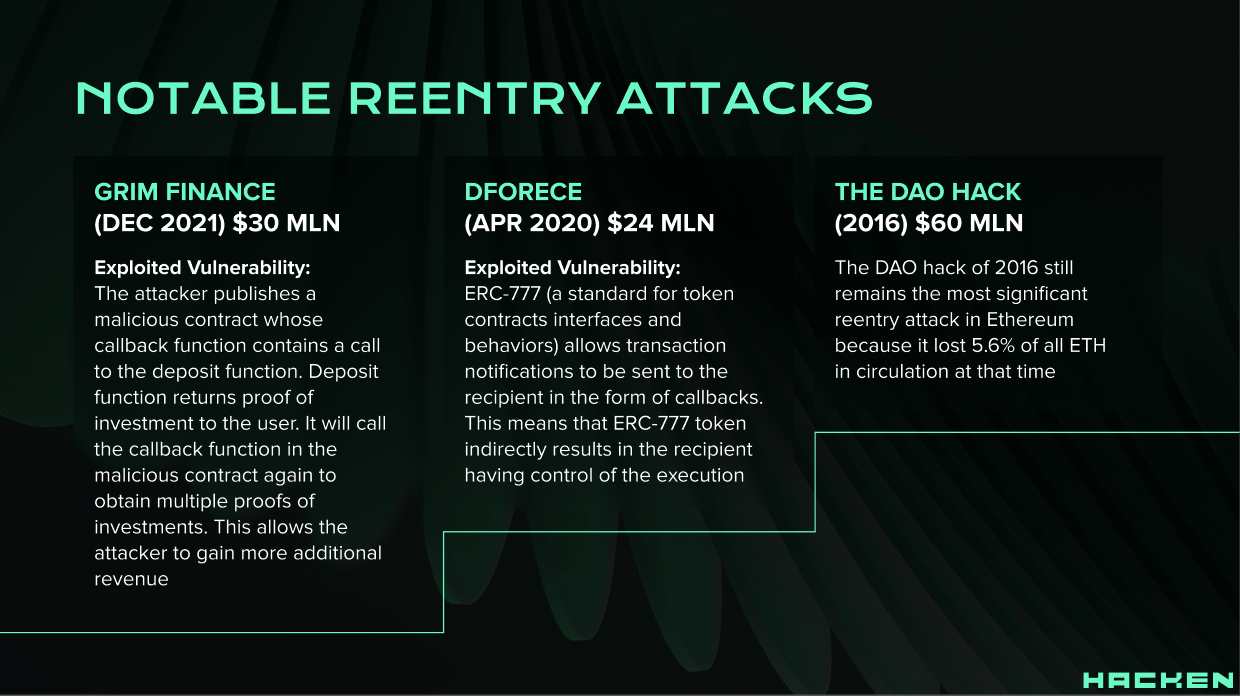
Smart Contract Attacks: The Most Memorable Blockchain Hacks of All Time - Nextrope - Your Trusted Partner for Blockchain Development and Advisory Services

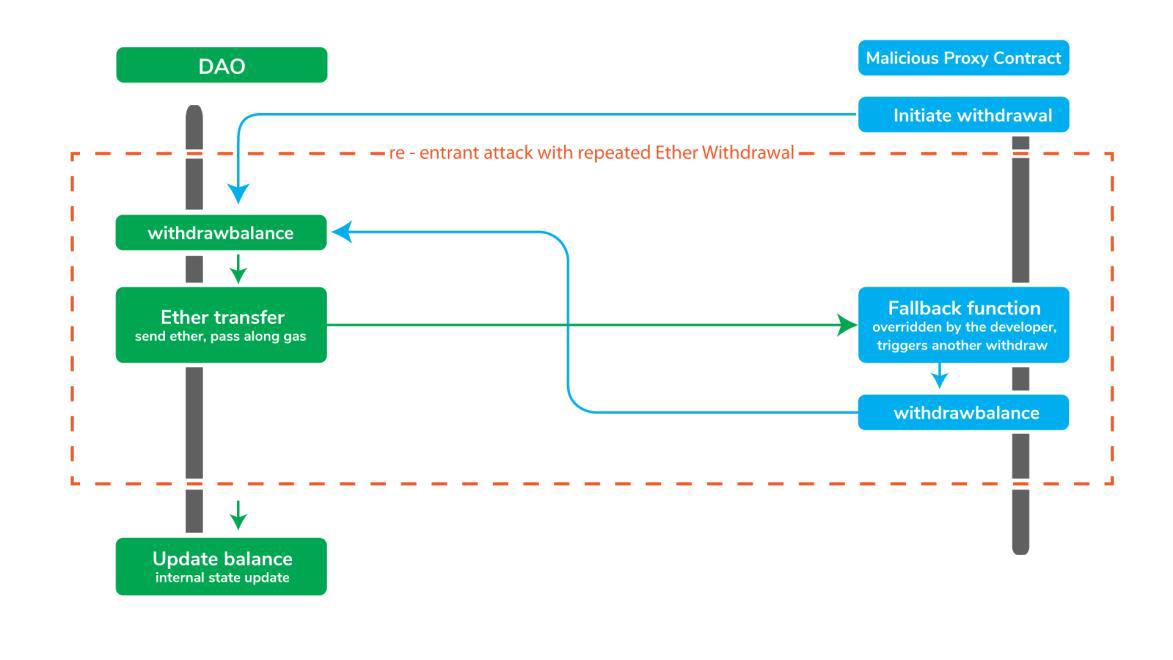
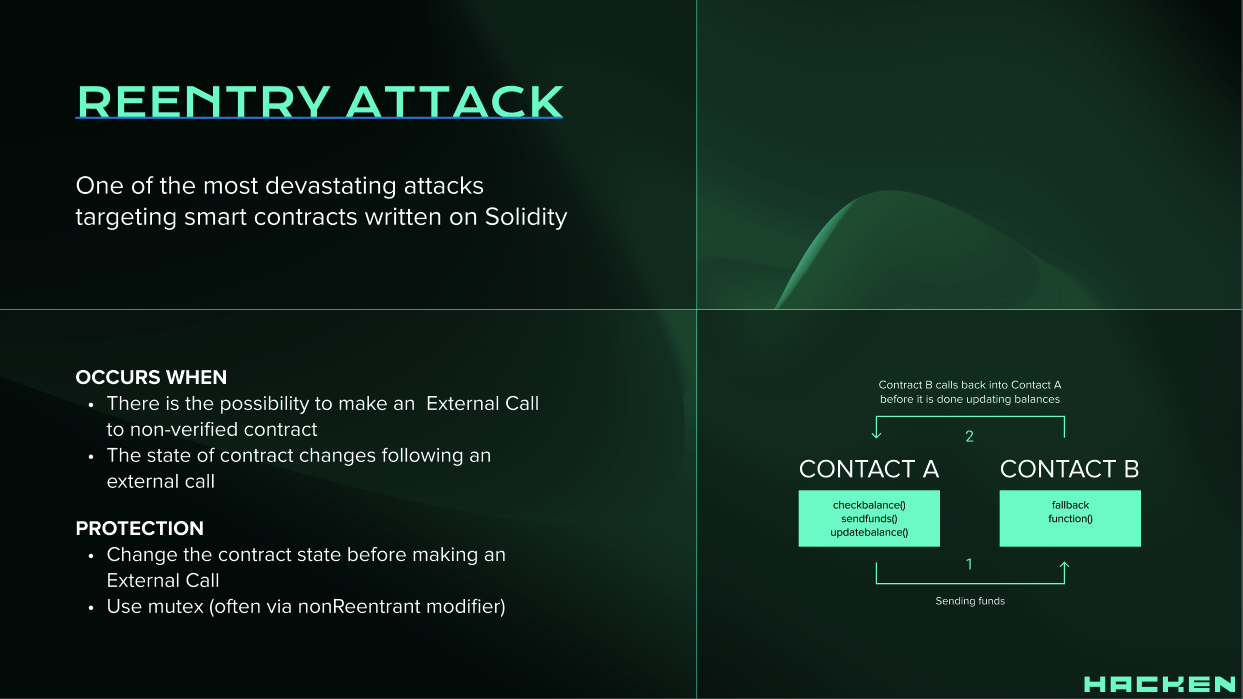
Chainlink on X: "Reentrancy attacks: A notorious attack vector for smart contracts. A reentrancy attack caused the infamous The DAO hack in 2016. Here's what a reentrancy attack is and how it

The number of attacks from smart contracts accounts for a significant... | Download Scientific Diagram

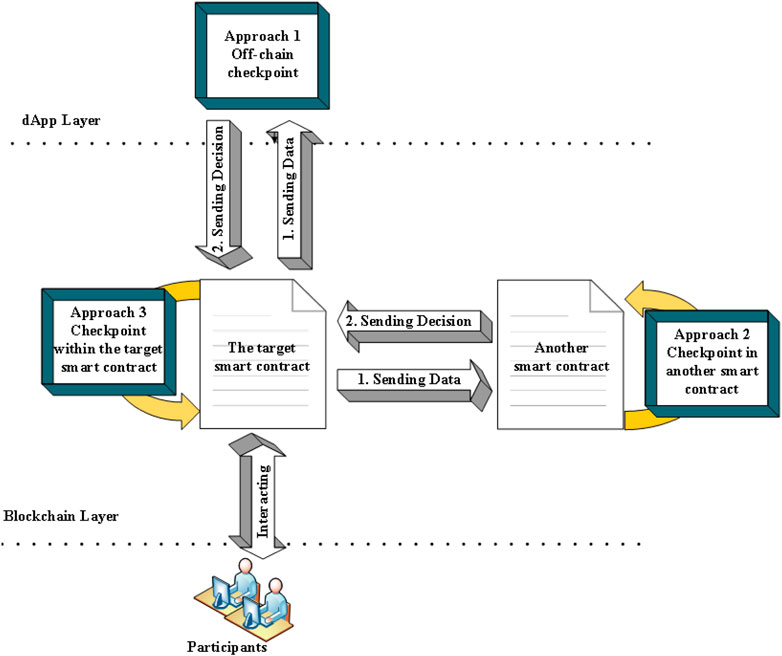
Machines | Free Full-Text | Securing Blockchain-Based Supply Chain Workflow against Internal and External Attacks

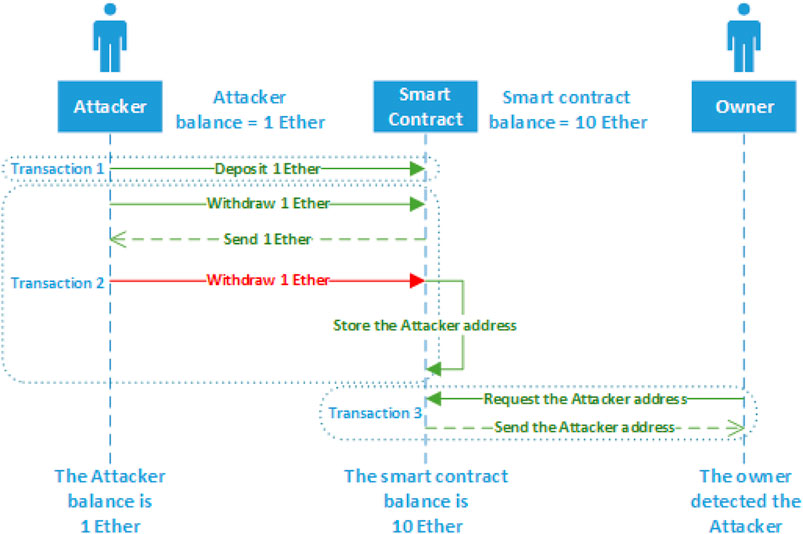
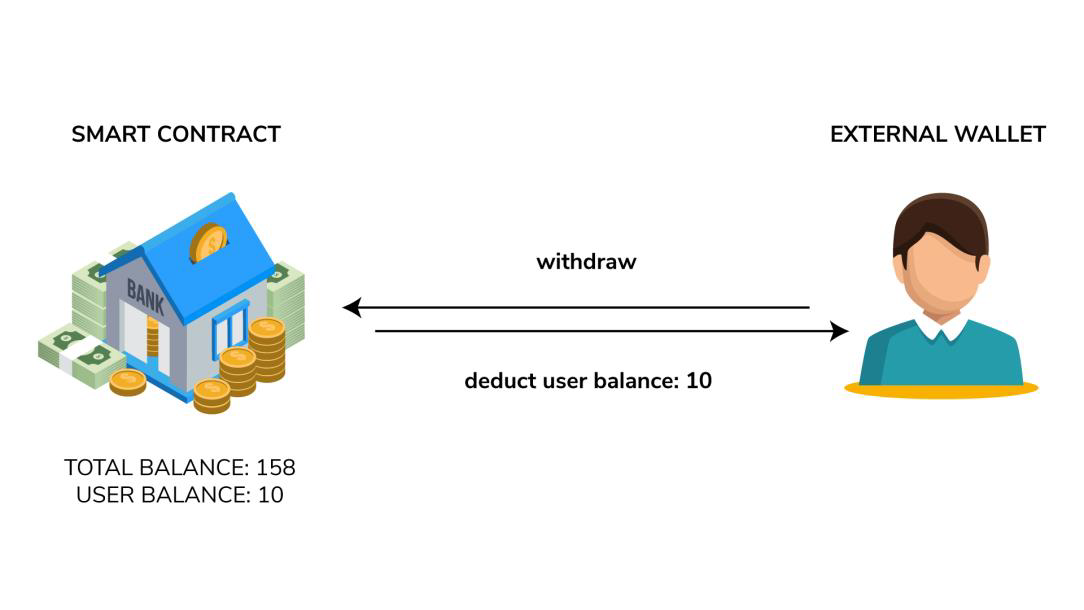
Reentrancy Attack: Understanding and Mitigating Vulnerabilities in Solidity Smart Contracts | by ismail | CoinsBench

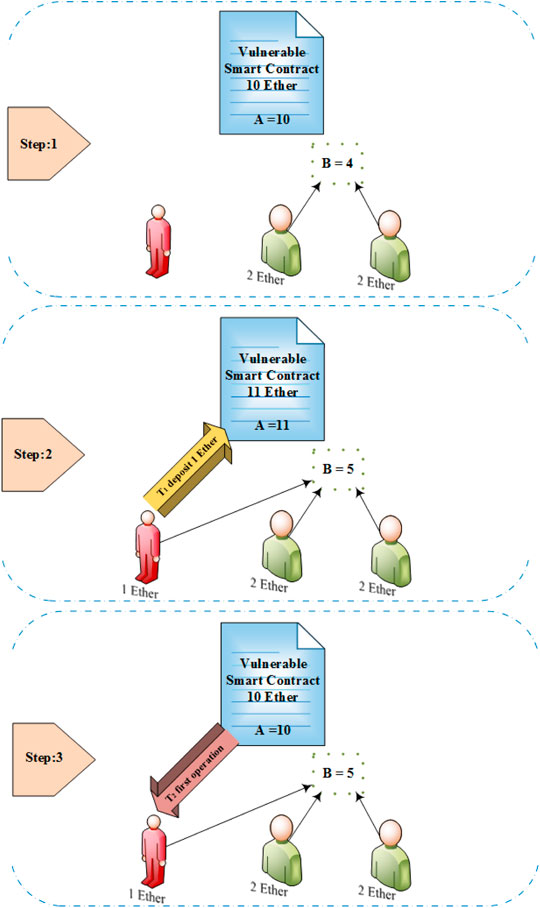
![PDF] Smart Contract: Attacks and Protections | Semantic Scholar PDF] Smart Contract: Attacks and Protections | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/5d30af04fa41ed28d91c621ab51c6f83d9df3296/5-Figure3-1.png)
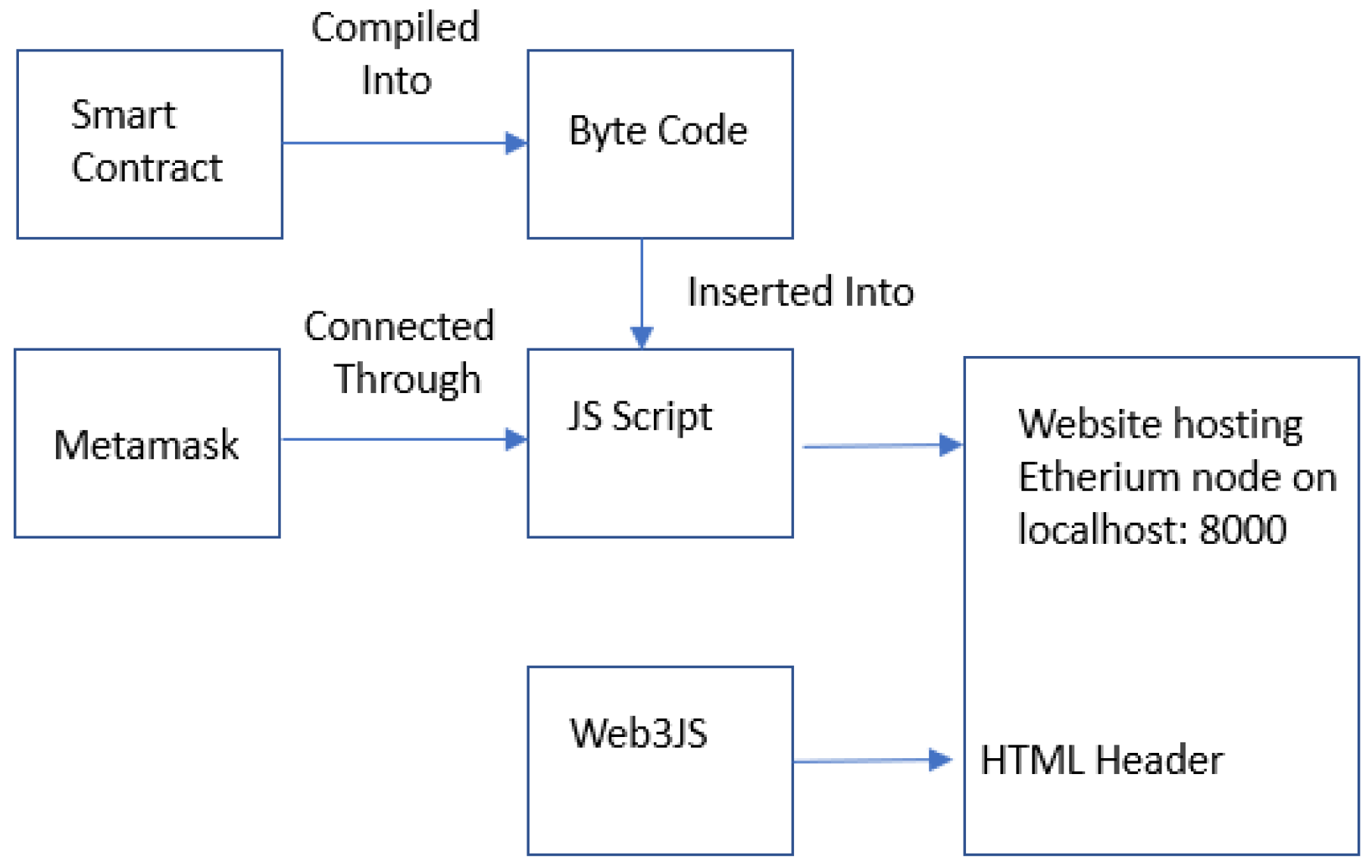





![PDF] Smart Contract: Attacks and Protections | Semantic Scholar PDF] Smart Contract: Attacks and Protections | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/5d30af04fa41ed28d91c621ab51c6f83d9df3296/4-Figure2-1.png)